【特訊】隨著社會數碼化轉型步伐不斷加快,各項智慧應用及生活場景逐步走入我們的生活,大量數據傳輸透過網絡進行交互,讓「網絡安全」變得尤為重要,作為基礎網絡營運商及智慧應用服務供應商,澳門電訊透過引進及投資網絡安全防護技術,守護澳門網絡安全,從而提升社會對網絡安全的重視程度,澳門電訊攜手合作夥伴,舉辦了「網絡安全」攻略分享會,分享現時流行的網絡攻擊形式及應對方案。 CTM「網絡安全」攻略分享會於上周五(七月九日)假澳門美高梅舉行,澳門電訊與Fortinet、ExclusiveNetworks、A10Networks、IUWorld及NSFOCUS公司代表,透過簡單生動的案例,分享網絡安全案例、現今主流的防護應用及技術,以及共同探討如何配合「網安法」,讓受監管的營運實體及機構合規運營以及避免網絡安全問題,「守護」線上應用、「防範」資料外洩,提高安全性以確保服務及業務的穩定。 A10Networks技術經理蕭漢明分享了澳門在今年上半年受到DDoS的威脅情況,以及如何透過CTM安全服務,在安全控制點上優化安全策略等。澳門電訊資訊科技高級經理鄭貴昌就網絡攻擊趨勢及案例進行分享。與會者分別來自政府、本地中小企業等,反映出社會對網絡安全的重視程度,未來,澳門電訊會繼續透過引進和研發更多安全應用,發揮好網絡把關人的角色,守護澳門網絡安全,以及助力各界提升網絡安全級別。
Author Archives: Micky Wong
IT Development to lead the way in GBA
Hong Kong, Guangdong and Macao have jointly launched the Greater Bay Area (GBA) International Information Technology Association, which aims to boost information technology (IT) development and application in the regions. The association plans to undertake related policy research work, setup communication and cooperation platforms for enterprises to enhance their regional connectivity, and nurture young ITContinueContinue reading “IT Development to lead the way in GBA”
Ridge Security Automated Penetration Testing Solution Delivers Advanced Post-Exploitation Techniques
Ridge Security, cutting-edge automated penetration testing solution provider, announces new capabilities in RidgeBot 3.4, for post-exploitation validation. This new release further differentiates RidgeBot from vulnerability scanners and 1-step auto-exploitation tools that are currently available and strengthens RidgeBot’s position as a true risk-based vulnerability management platform. Post-exploitation operations are advanced hacking techniques, often utilized by an APT (AdvancedContinueContinue reading “Ridge Security Automated Penetration Testing Solution Delivers Advanced Post-Exploitation Techniques”
Integrating Cybersecurity into Business Continuity Planning
Organizations can’t afford to wait until a threat is identified to start worrying about their #cybersecurity. Measures must be integrated throughout the entire process! Learn more about integrating cybersecurity into business continuity planning –> http://ow.ly/yXya50EKVo5
Kaspersky has recently published the latest installment of its quarterly summaries of advanced persistent threat (APT) activity.
The most remarkable findings In December, SolarWinds, a well-known IT managed services provider, fell victim to a sophisticated supply-chain attack. The company’s Orion IT, a solution for monitoring and managing customers’ IT infrastructure, was compromised. This resulted in the deployment of a custom backdoor, named Sunburst, on the networks of more than 18,000 SolarWinds customers,ContinueContinue reading “Kaspersky has recently published the latest installment of its quarterly summaries of advanced persistent threat (APT) activity.”
XDR Delivers Significant Performance Improvement over SIEM
In every SOC environment, there are two key metrics that demonstrate efficiency and effectiveness: Mean Time to Detection (MTTD) and Mean Time to Remediation (MTTR). The risk and exposure from any cyber threat can be reduced significantly by improving these metrics. Stellar Cyber recently completed a study with its MSP and MSSP partners, to determine how much our OpenContinueContinue reading “XDR Delivers Significant Performance Improvement over SIEM”
勒索軟件入侵校園 NCSC警告攻擊將大增
上月教育行業受勒索軟件影響之後,英國國家網絡安全中心(National Cyber Security Center, NCSC)就如何保護網絡免受網絡犯罪分子侵擾提出建議,並警告針對學校、學院和大學的勒索軟件攻擊激增。 政府通訊信總部(Government Communications Headquarters, GCHQ)網絡安全部門的警報指,在過去一個月中,針對教育的勒索軟件攻擊數量激增,而與此同時,學校亦正準備恢復面授課程。 勒索軟件會攻擊加密伺服器和數據,從而阻止組織提供服務,在這種情況下,網絡罪犯企圖令學校和大學因要維持教學,而屈服於勒索要求,並要求受害者以比特幣支付贖金,換取恢復網絡的解密密鑰。而在最近受影響的教育機構中,勒索軟件令學生課程、學校財務記錄以及與 COVID-19 測試的有關數據損失。這些黑客威脅如果他們沒有得到贖金,便會發布被盜數據。 資料來源:https://zd.net/3tJKkDa
Principles for Board Governance of Cyber Risk
Cyber risk is among the top risks facing businesses today, and it has become clear that boards, especially, need stronger foundations to govern cyber risks effectively. Companies that effectively manage the entire portfolio of risks, including cyber, do better in the marketplace. This paper, published by the World Economic Forum, is designed as a reference forContinueContinue reading “Principles for Board Governance of Cyber Risk”
CISA Strongly Urges All Organizations to Immediately Address Microsoft Exchange Vulnerabilities
CISA on 8rd March, 2021 has published a Remediating Microsoft Exchange Vulnerabilities web page that strongly urges all organizations to immediately address the recent Microsoft Exchange Server product vulnerabilities. As exploitation of these vulnerabilities is widespread and indiscriminate, CISA strongly advises organizations follow the guidance laid out in the web page. The guidance provides specific steps forContinueContinue reading “CISA Strongly Urges All Organizations to Immediately Address Microsoft Exchange Vulnerabilities”
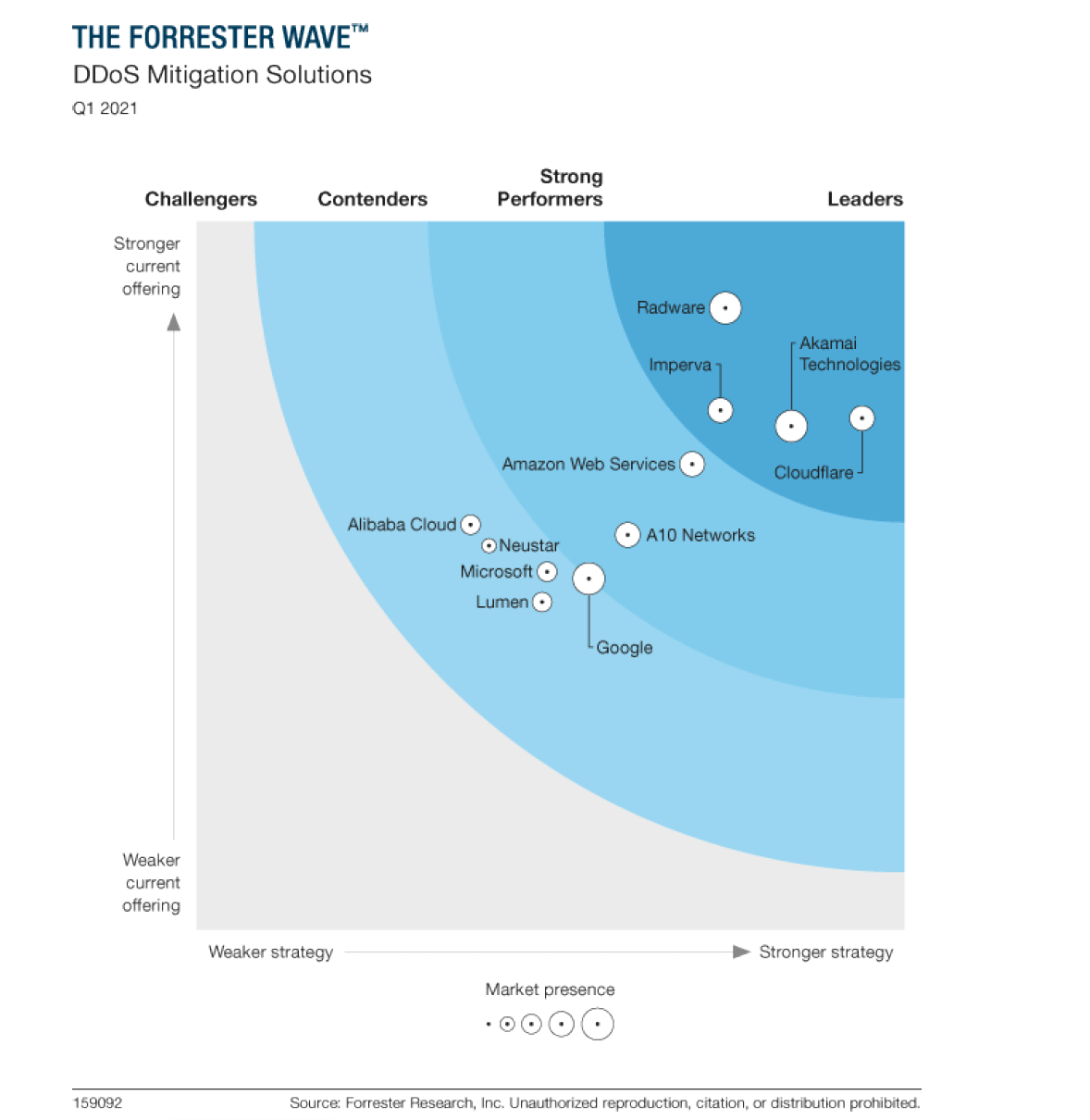
The Forrester Wave™: DDoS Mitigation Solutions, Q1 2021
Forrester’s research uncovered a market in whichCloudflare, Radware, Akamai Technologies, andImperva are Leaders; Amazon Web Servicesand A10 Networks are Strong Performers; andGoogle, Microsoft, Alibaba Cloud, Neustar, andLumen are Contenders.